Lessons for CEOs from the Saudi Aramco Breach
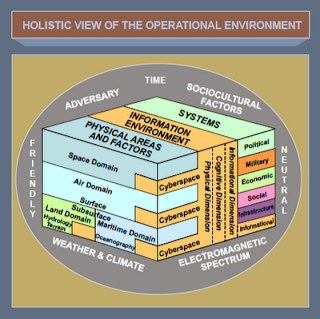 |
| Source: Joint Intelligence Preparation of the Operational Environment (JP 2-01.3) |
1. The Conventional Cyber Threat Landscape Is Too Narrowly Viewed
Most if not all companies' security operations centers are monitoring for the now conventional Advanced Persistant Threat-style of attack and their defensive tactics are geared towards interrupting that attack by use of an "intrusion kill chain". The attack suffered by Saudi Aramco didn't fit this model, and hence would have been completely missed by most of the world's largest companies. A multinational corporation must perform a comprehensive review of its entire threat landscape prior to designing its security framework. This includes evaluating its network exposure through its offices in foreign nations, its vendors (including U.S. vendors) and their relationships with the governments of potential adversary states, compromise of its senior executives while traveling, legal access to its intellectual property (i.e., source code) by foreign intelligence services (FIS) if the company conducts business in those same states, and so on. None of these potential attack vectors rely on spear phishing, social engineering, or other commonly watched-for schemes nor would any of them be caught by the vast array of security software being shopped by vendors today. While MNCs are busy sticking their fingers into the APT holes in their dike, State FIS are quietly re-routing the entire river behind the dike.
2. Companies Need To Pay Closer Attention to the Insider Threat
It's my understanding from a confidential source that the initial infection vector wasn't through a spear phishing attack but instead was via a Shamoon-infected USB stick which was inserted into a workstation in one of Aramco's foreign offices. This required the cooperation of an insider which, in fact, has been a serious and growing threat vector for a number of years. It's also one that conventional defenses like anti-virus, firewalls, and IPS/IDS cannot stop and that more sophisticated defenses like encryption and virtualization are not entirely effective against. This threat vector requires a more specific and potentially intrusive security posture which monitors for early signals that an insider typically presents prior to his malicious act.
3. Companies Cannot Keep a Dedicated Adversary Out of their Network
Saudi Aramco's attackers have threatened another attack today, the 25th at 2100 GMT to prove their ability to cause harm to the company. And the fact is, they can. This is a David and Goliath scenario if there ever was one. The world's wealthiest company cannot stop a small group from successfully performing an attack. No one can. Therefore, the correct course of action for not only Aramco's CEO but every CEO is to focus on being able to absorb an attack and not have it affect its critical operations. This requires making choices between what's critical and what isn't. Keeping your website up 24/7 in the face of a DDOS attack isn't critical. Keeping your oil production from being interrupted is. Keeping your intellectual property from being stolen is. An MNC's CEO and Board of Directors need to perform a difficult but necessary inventory of their corporation's assets and divide them into critical and non-critical groups. Different security protocols and controls need to be applied based upon criticality and resiliency.
While I haven't had the privilege of consulting with Aramco's leadership on their breach, my team and I have provided counsel for other MNCs and the above guidance is a very high level overview of our recommendations in those cases. Obviously, the devil is in the details and specifics on how to implement the above guidance will vary on a company by company basis. The bottom line is that if a company's board still believes that their company is safe from being breached, they have their heads up their collective asses.
RELATED:
Was Iran Responsible for Saudi Aramco's Network Attack?
Saudi Aramco's Security Nightmare: Poor Design, Corrupt Contractors, and More
Operations Security at Saudi Aramco? Zero.





I believe one of the best recommendations is to have a dedicated server for each dept. So, these dedicated servers are not connected to the network only when for backing up.
ReplyDelete