Where's the "Strike" in CrowdStrike?
I've had mixed feelings about CrowdStrike from the moment that it launched in stealth status last February. On the one hand, I'm a big fan of how Shawn Henry (President of CrowdStrike Services) helped move the FBI from a terribly incompetent position vis a vis cyber investigations (circa 2005-06) to one of the world's premiere cyber investigative bodies in just a few short years. On the other hand, I detest McAfee and I've openly ridiculed their so-called "reports" on more than one occasion. As an Israeli friend of mine put it, Anti-Virus companies aren't security companies. And I might add, they aren't intelligence organizations either. The one thing that McAfee does have are rich executives, including CrowdStrike co-founders Gregg Marston, Dmitri Alperovich, and George Kurtz who arranged CrowdStrike's $26 million Series A funding from Warburg Pincus where Kurtz was an Executive-in-Residence after McAfee was acquired by Intel for $7.86 Billion in cash.
A LinkedIn search shows that the company has been attracting/recruiting lots of talent but so far they haven't announced much in the way of a product line. They did launch an open source reverse-engineering portal called CrowdRE which lets anyone play with a highly regarded Disassembler called IDAPro in a cloud-based server. The benefit to CrowdStrike is that in exchange for providing the portal, it can quickly grow a database of reverse-engineered malware that it can utilize on behalf of its paying customers.
The question that I and others have been asking since last February's launch has to do with the "offensive" hook that CrowdStrike advertises via its tag line "You don't have a malware problem. You have an adversary problem"(tm). The company website claims to offer "Enterprise Adversary Assessment" where "we identify the adversary and find out what they're after." And how do they do that? Back to the website: "Through hunting operations, including host-based detection, threat-specific network analysis, and victim threat profiling".
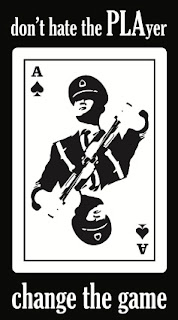
In case you have any doubt as to who the adversary is, their cool t-shirt makes it pretty clear:
Gee, what a surprise. CrowdStrike has determined that the adversary is China. And that's a continuation of the piss-poor intelligence that Dmitri Alperovich published while at McAfee: Operation Shady Rat (China), Operation Aurora (China) and Operation Night Dragon (China). There's over 30 nation states developing computer network attack, defense, and exploitation capabilities and at least a dozen that are highly proficient and actively conducting cyber espionage yet somehow McAfee's "intelligence analysts" only see China. Not Israel, Russia, Taiwan, France, Germany, or South Korea - just the PRC. In a video interview, CrowdStrike's Director of Intelligence Adam Meyers talks about identifying adversaries via toolmarks and the usual TTPs that every so-called cyber intelligence firm narrowly focuses their attention on but that's not analysis (See Michael Tanji's recent article on the subject "Malware Analysis: The Danger of Connecting The Dots"). In the intelligence community, that's a cognitive trap known as target fixation. If after looking at all of the technical parameters, the only nation state that you see is China, you need to find another job because you suck as an intelligence analyst.
Getting back to CrowdStrike's "offensive" marketing theme, in Shawn Henry's keynote at BlackHat last summer, he made it clear that CrowdStrike wasn't advocating hacking back; that such activities were still illegal. CrowdStrike's latest high profile FBI hire Steven Chabinsky has also made it clear that the laws currently don't support even something as mild as a company encrypting its own data found on a foreign server. So what's the point in promoting a "take the fight to the adversary" approach when it's impossible to do in the current legal climate?
The bottom line is that, in my opinion, CrowdStrike cannot currently deliver anything unique in the infosec space that Mandiant and other companies aren't already doing unless it significantly improves its sources and methods regarding identifying adversary state and non-state actors and pushes the envelope on active defense. It's not enough to have a cool t-shirt that says "Change the Game". They literally have to do it.
A LinkedIn search shows that the company has been attracting/recruiting lots of talent but so far they haven't announced much in the way of a product line. They did launch an open source reverse-engineering portal called CrowdRE which lets anyone play with a highly regarded Disassembler called IDAPro in a cloud-based server. The benefit to CrowdStrike is that in exchange for providing the portal, it can quickly grow a database of reverse-engineered malware that it can utilize on behalf of its paying customers.
The question that I and others have been asking since last February's launch has to do with the "offensive" hook that CrowdStrike advertises via its tag line "You don't have a malware problem. You have an adversary problem"(tm). The company website claims to offer "Enterprise Adversary Assessment" where "we identify the adversary and find out what they're after." And how do they do that? Back to the website: "Through hunting operations, including host-based detection, threat-specific network analysis, and victim threat profiling".
In case you have any doubt as to who the adversary is, their cool t-shirt makes it pretty clear:
Gee, what a surprise. CrowdStrike has determined that the adversary is China. And that's a continuation of the piss-poor intelligence that Dmitri Alperovich published while at McAfee: Operation Shady Rat (China), Operation Aurora (China) and Operation Night Dragon (China). There's over 30 nation states developing computer network attack, defense, and exploitation capabilities and at least a dozen that are highly proficient and actively conducting cyber espionage yet somehow McAfee's "intelligence analysts" only see China. Not Israel, Russia, Taiwan, France, Germany, or South Korea - just the PRC. In a video interview, CrowdStrike's Director of Intelligence Adam Meyers talks about identifying adversaries via toolmarks and the usual TTPs that every so-called cyber intelligence firm narrowly focuses their attention on but that's not analysis (See Michael Tanji's recent article on the subject "Malware Analysis: The Danger of Connecting The Dots"). In the intelligence community, that's a cognitive trap known as target fixation. If after looking at all of the technical parameters, the only nation state that you see is China, you need to find another job because you suck as an intelligence analyst.
Getting back to CrowdStrike's "offensive" marketing theme, in Shawn Henry's keynote at BlackHat last summer, he made it clear that CrowdStrike wasn't advocating hacking back; that such activities were still illegal. CrowdStrike's latest high profile FBI hire Steven Chabinsky has also made it clear that the laws currently don't support even something as mild as a company encrypting its own data found on a foreign server. So what's the point in promoting a "take the fight to the adversary" approach when it's impossible to do in the current legal climate?
The bottom line is that, in my opinion, CrowdStrike cannot currently deliver anything unique in the infosec space that Mandiant and other companies aren't already doing unless it significantly improves its sources and methods regarding identifying adversary state and non-state actors and pushes the envelope on active defense. It's not enough to have a cool t-shirt that says "Change the Game". They literally have to do it.





Comments
Post a Comment