Search This Blog
Evolving Hostilities in the Global Cyber Commons
Posts
Showing posts from July, 2013
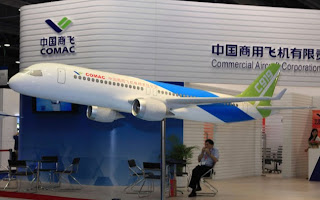
Aviation companies twice as likely to be hacked if they do business in China
- Get link
- Other Apps
Taking a Deep Dive into China's Cyber Threat Landscape
- Get link
- Other Apps
Chinese and Russian Information Security and Aeronautics R&D Luncheon
- Get link
- Other Apps
My First-hand Experience with China's Most Successful Technology Transfer Campaign (better than hacking)
- Get link
- Other Apps