Search This Blog
Evolving Hostilities in the Global Cyber Commons
Posts
Showing posts from November, 2011
Dark Cloud Rising: Cloud Services are Becoming the Attackers' Preferred Target
- Get link
- X
- Other Apps
Actress, Banker, Soldier, Spy: Announcing Suits and Spooks II
- Get link
- X
- Other Apps
Rep. Mike Rogers Needs To Re-Think His China Tactics
- Get link
- X
- Other Apps
The Russian Internet (Runet) Becomes More Opaque
- Get link
- X
- Other Apps
Latest FBI Statement On Alleged Illinois Water Company Attack
- Get link
- X
- Other Apps
Who's Selling Huawei Products To The U.S. Government?
- Get link
- X
- Other Apps
Google's Finland Data Center Was A Security-Savvy Move
- Get link
- X
- Other Apps
Symantec Sells Its Stake In Huawei-Symantec Joint Venture
- Get link
- X
- Other Apps
Forbes, Nike, and the Endorsement of Child Rape
- Get link
- X
- Other Apps
Words Matter: Why Derek Bambauer's Wrong on Cyber Terrorism
- Get link
- X
- Other Apps
Why DARPA Is Clueless About Securing Cyberspace
- Get link
- X
- Other Apps
A Review of the NCIX Report on Foreign Economic Collection and Industrial Espionage
- Get link
- X
- Other Apps
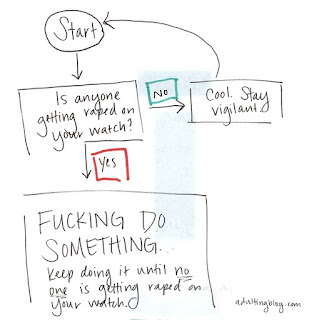
Decision Tree for Potential #OpCartel Participants
- Get link
- X
- Other Apps